在 Kubernetes 中使用 Nginx Ingress Controller,可以实现黑名单和白名单的功能来控制哪些请求被接受或拒绝。黑名单用于禁止特定 IP 地址或 IP 地址范围的请求,而白名单用于仅允许特定 IP 地址或 IP 地址范围的请求通过。
一、配置黑名单¶
1.配置黑名单禁止某一个或某一段IP,需要在Nginx Ingress的ConfigMap中配置,比如将192.168.1.34(多个配置使用逗号分隔)添加至黑名单
[root@k8s-master01 ~]# cd ingress-nginx
[root@k8s-master01 ingress-nginx]# vim values.yaml
config:
block-cidrs: 192.168.100.34
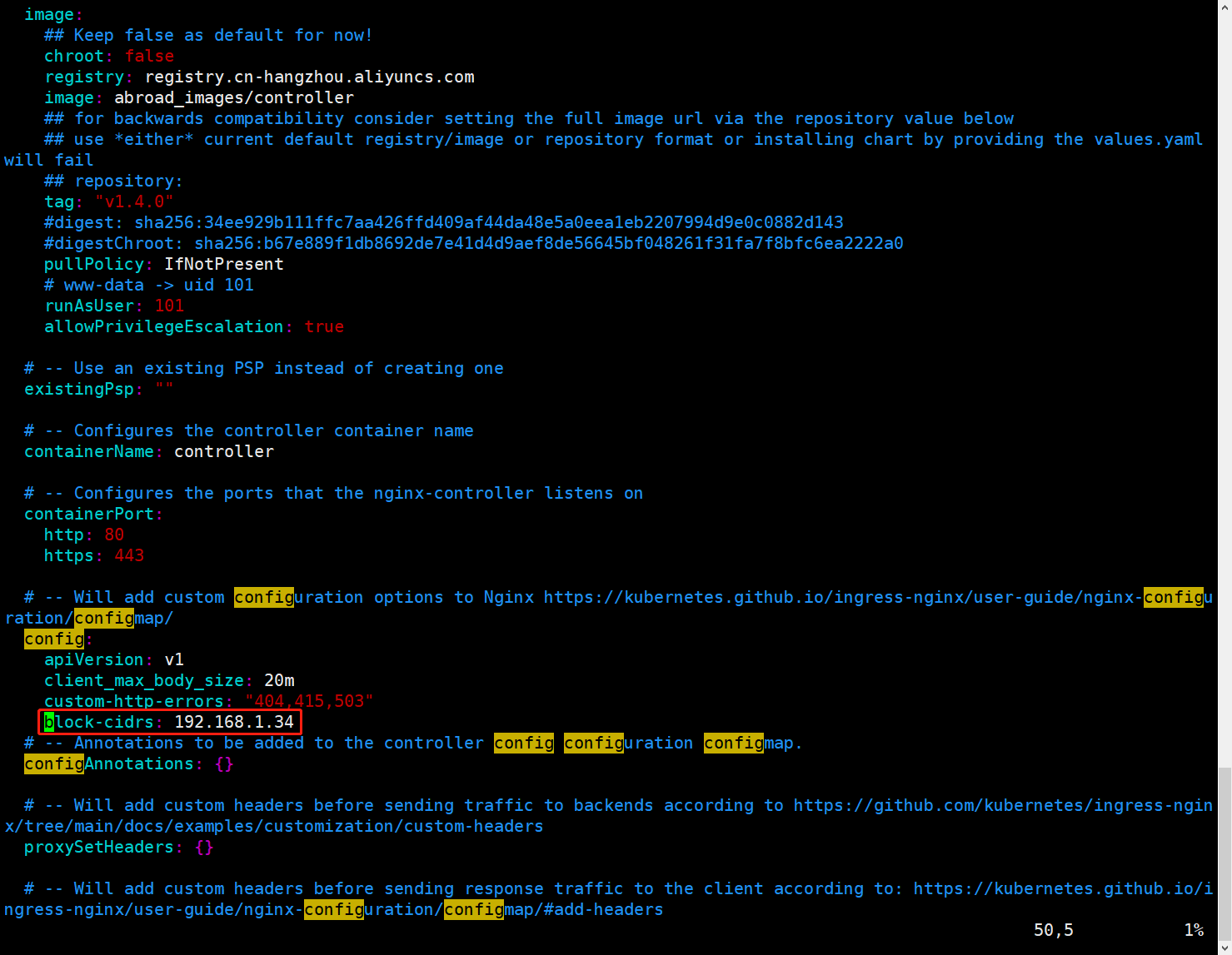
说明:config下面的其他配置是上面实验遗留配置
2.滚动更新 Nginx Ingress
在滚动更新之前,先测试192.168.1.34是否可以访问m.test.com,方便后面验证,观察到可以正常访问
[root@k8s-master01 ingress-nginx]# ssh k8s-node01
[root@k8s-node01 ~]# ip -4 a | grep 1.34
inet 192.168.1.34/24 brd 192.168.1.255 scope global ens33
[root@k8s-node01 ~]# curl -H "Host:m.test.com" 192.168.1.35 -I
HTTP/1.1 200 OK
Date: Mon, 31 Jul 2023 12:53:57 GMT
Content-Type: text/html
Content-Length: 62
Connection: keep-alive
Last-Modified: Thu, 12 Aug 2021 08:23:47 GMT
ETag: "6114da93-3e"
Accept-Ranges: bytes
接下来开始滚动更新
[root@k8s-master01 ~]# cd ingress-nginx
[root@k8s-master01 ingress-nginx]# helm upgrade ingress-nginx -n ingress-nginx .
3.再次使用 192.168.1.34 主机再次访问,发现该 IP 已经被禁止
[root@k8s-master01 ingress-nginx]# ssh k8s-node01
[root@k8s-node01 ~]# ip -4 a | grep 1.34
inet 192.168.1.34/24 brd 192.168.1.255 scope global ens33
[root@k8s-node01 ~]# curl -H "Host:m.test.com" 192.168.1.35 -I
HTTP/1.1 403 Forbidden
Date: Mon, 31 Jul 2023 13:10:24 GMT
Content-Type: text/html
Content-Length: 146
Connection: keep-alive
使用192.168.1.31 主机进行对比访问,发现该 IP 可以正常访问
[root@k8s-master01 ingress-nginx]# ip -4 a | grep 1.31
inet 192.168.1.31/24 brd 192.168.1.255 scope global ens33
[root@k8s-master01 ingress-nginx]# curl -H "Host:m.test.com" 192.168.1.35 -I
HTTP/1.1 200 OK
Date: Mon, 31 Jul 2023 13:10:56 GMT
Content-Type: text/html
Content-Length: 62
Connection: keep-alive
Last-Modified: Thu, 12 Aug 2021 08:23:47 GMT
ETag: "6114da93-3e"
Accept-Ranges: bytes
二、配置白名单¶
白名单表示只允许某个 IP 可以访问,直接在 yaml 文件中配置即可(也可以通过 ConfigMap 配置),比如只允许 192.168.1.31 访问,只需要添加一个 nginx.ingress.kubernetes.io/whitelistsource-range 注释即可。
1.在192.168.1.31 和192.168.1.32主机上分别进行访问测试,观察到二者都成功访问
在192.168.1.31 主机上进行访问测试
[root@k8s-master01 ingress-nginx]# ip -4 a | grep 1.31
inet 192.168.1.31/24 brd 192.168.1.255 scope global ens33
[root@k8s-master01 ingress-nginx]# curl -H "Host:test.com" 192.168.1.35 -I
HTTP/1.1 200 OK
Date: Mon, 31 Jul 2023 13:16:23 GMT
Content-Type: text/html
Content-Length: 30
Connection: keep-alive
Last-Modified: Thu, 12 Aug 2021 08:21:09 GMT
ETag: "6114d9f5-1e"
Accept-Ranges: bytes
在192.168.1.32 主机上进行访问测试
[root@k8s-master01 ingress-nginx]# ssh k8s-master02
[root@k8s-master02 ~]# ip a | grep 1.32
inet 192.168.1.32/24 brd 192.168.1.255 scope global ens33
inet 10.0.0.1/32 scope global kube-ipvs0
[root@k8s-master02 ~]# curl -H "Host:test.com" 192.168.1.35 -I
HTTP/1.1 200 OK
Date: Mon, 31 Jul 2023 13:18:33 GMT
Content-Type: text/html
Content-Length: 30
Connection: keep-alive
Last-Modified: Thu, 12 Aug 2021 08:21:09 GMT
ETag: "6114d9f5-1e"
Accept-Ranges: bytes
2.修改laptop-ingress.yaml文件
在原来的基础上添加如下配置:
nginx.ingress.kubernetes.io/whitelist-source-range: 192.168.1.31
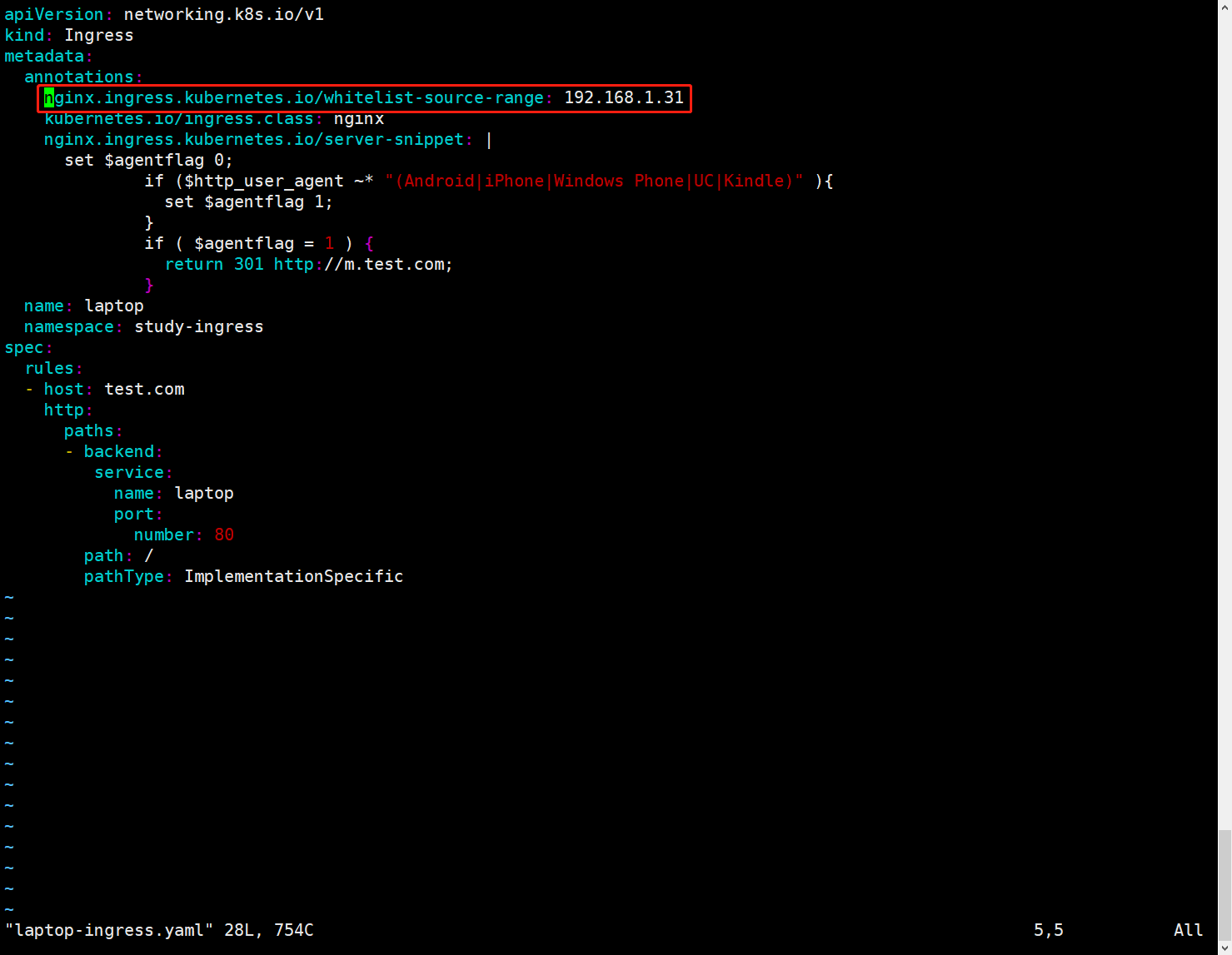
添加完配置文件如下:
[root@k8s-master01 ~]# vim laptop-ingress.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
annotations:
nginx.ingress.kubernetes.io/whitelist-source-range: 192.168.1.31
kubernetes.io/ingress.class: nginx
nginx.ingress.kubernetes.io/server-snippet: |
set $agentflag 0;
if ($http_user_agent ~* "(Android|iPhone|Windows Phone|UC|Kindle)" ){
set $agentflag 1;
}
if ( $agentflag = 1 ) {
return 301 http://m.test.com;
}
name: laptop
namespace: study-ingress
spec:
rules:
- host: test.com
http:
paths:
- backend:
service:
name: laptop
port:
number: 80
path: /
pathType: ImplementationSpecific
3.更新该 Ingress
[root@k8s-master01 ~]# kubectl replace -f laptop-ingress.yaml
4.在192.168.1.31 和192.168.1.32主机上分别进行访问测试,观察到192.168.1.31成功访问,192.168.1.32主机访问失败
[root@k8s-master01 ~]# curl -H "Host:test.com" 192.168.1.35 -I
HTTP/1.1 200 OK
Date: Mon, 31 Jul 2023 13:24:29 GMT
Content-Type: text/html
Content-Length: 30
Connection: keep-alive
Last-Modified: Thu, 12 Aug 2021 08:21:09 GMT
ETag: "6114d9f5-1e"
Accept-Ranges: bytes
[root@k8s-master01 ~]# ssh k8s-master02
[root@k8s-master02 ~]# curl -H "Host:test.com" 192.168.1.35 -I
HTTP/1.1 403 Forbidden
Date: Mon, 31 Jul 2023 13:24:56 GMT
Content-Type: text/html
Content-Length: 146
Connection: keep-alive
