来自AI助手的总结
演示Kubernetes RBAC为用户分配命名空间查看、日志、执行和删除权限
一、创建通用权限
1.1 创建通用权限-list
[root@k8s-master01 study]# vim namespace-readonly.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: namespace-readonly
rules:
- apiGroups:
- ""
resources:
- namespaces
verbs:
- get
- list
- watch
- apiGroups:
- metrics.k8s.io
resources:
- pods
verbs:
- get
- list
- watch
[root@k8s-master01 study]# kubectl create -f namespace-readonly.yaml
1.2 创建通用权限-delete
[root@k8s-master01 study]# vim pod-delete.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: pod-delete
rules:
- apiGroups:
- ""
resources:
- pods
verbs:
- get
- list
- delete
[root@k8s-master01 study]# kubectl create -f pod-delete.yaml
1.3 创建通用权限-exec
[root@k8s-master01 study]# vim pod-exec.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: pod-exec
rules:
- apiGroups:
- ""
resources:
- pods
verbs:
- get
- list
- apiGroups:
- ""
resources:
- pods/exec
verbs:
- create
[root@k8s-master01 study]# kubectl create -f pod-exec.yaml
1.4 创建通用权限-log
[root@k8s-master01 study]# vim pod-log.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: pod-log
rules:
- apiGroups:
- ""
resources:
- pods
- pods/log
verbs:
- get
- list
- watch
[root@k8s-master01 study]# kubectl create -f pod-log.yaml
二、创建用户管理命名空间
[root@k8s-master01 study]# kubectl create ns kube-users
三、创建用户
[root@k8s-master01 study]# kubectl create sa user1 -n kube-users
[root@k8s-master01 study]# kubectl create sa user2 -n kube-users
四、获取两个用户的token
4.1 获取user1用户的token
[root@k8s-master01 study]# kubectl get secret -n kube-users
NAME TYPE DATA AGE
default-token-wwngg kubernetes.io/service-account-token 3 5m42s
user1-token-vsv6v kubernetes.io/service-account-token 3 14s
user2-token-bkwhd kubernetes.io/service-account-token 3 11s
[root@k8s-master01 study]# kubectl describe secret dotbalo-token-mnj4h -n kube-users
Name: user1-token-vsv6v
Namespace: kube-users
Labels: <none>
Annotations: kubernetes.io/service-account.name: user1
kubernetes.io/service-account.uid: 3c2148f0-3e8e-4bbb-a8f5-c134e5625a9d
Type: kubernetes.io/service-account-token
Data
====
token: eyJhbGciOiJSUzI1NiIsImtpZCI6IjNISFg5NWpEa0VIYXMyMG5YSGdaaHhDUVVMQXgzYzdQbmlCWmZSeU1GSG8ifQ.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlLXVzZXJzIiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImRvdGJhbG8tdG9rZW4tbW5qNGgiLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC5uYW1lIjoiZG90YmFsbyIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50LnVpZCI6IjNjMjE0OGYwLTNlOGUtNGJiYi1hOGY1LWMxMzRlNTYyNWE5ZCIsInN1YiI6InN5c3RlbTpzZXJ2aWNlYWNjb3VudDprdWJlLXVzZXJzOmRvdGJhbG8ifQ.kp8KzdHqy5dnSHOW7yQET4k6ad_1Fe1EYd7tjUAovYwNDxgw_bjfUivvxZbJXCvpnSAFWAsf8vaW7DHC4GH9nQ-nRZUMoNFUTuE1v1_NiS-7IqQ6zOOzBMfMeW_GuZUpaBbQUTmQCIJ2-z8L2ZAVjxoxSfhTMJ5c4E977644GO5frncazwC0sb2PweR3h2soWKWXYIvr_e2LQTByTWBT7ldMC7rTRcbVsK4-J9eULY-6v9zlNiGbLyQOzcQvLmjklJpTskqcYGo9sNhtblROhMqvCT9iBybgPNEfSHZHABn57ewcG5os0_5wsK88IdbVOjjT-jtYrkDdM1mlg-Z9-A
ca.crt: 1099 bytes
namespace: 10 bytes
4.2 获取user2用户的token
[root@k8s-master01 study]# kubectl get secret -n kube-users
NAME TYPE DATA AGE
default-token-wwngg kubernetes.io/service-account-token 3 5m42s
user1-token-vsv6v kubernetes.io/service-account-token 3 14s
user2-token-bkwhd kubernetes.io/service-account-token 3 11s
[root@k8s-master01 study]# kubectl describe secret dukuan-token-ntcbr -n kube-users
Name: user2-token-bkwhd
Namespace: kube-users
Labels: <none>
Annotations: kubernetes.io/service-account.name: user2
kubernetes.io/service-account.uid: 13b798c1-93cf-4619-a458-6e190618649f
Type: kubernetes.io/service-account-token
Data
====
namespace: 10 bytes
token: eyJhbGciOiJSUzI1NiIsImtpZCI6IjNISFg5NWpEa0VIYXMyMG5YSGdaaHhDUVVMQXgzYzdQbmlCWmZSeU1GSG8ifQ.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlLXVzZXJzIiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImR1a3Vhbi10b2tlbi1udGNiciIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkdWt1YW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiIxM2I3OThjMS05M2NmLTQ2MTktYTQ1OC02ZTE5MDYxODY0OWYiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6a3ViZS11c2VyczpkdWt1YW4ifQ.H06tdQIZ-JcWZBjysnq8NvcJ-ITzZd7VG1oHujRLgOye-YD4OEevDEFb_GvxgfDyYJSyED1ByWbxcwHY0_0pS1Rj-SGGuwC0arGnT-Z45QcTLXzcTKx2DBc8Ttae3AwYS_FOgDBhfv-E5iQXQzX5dOPFiRktJcQgq9WdRVcV2J6AK0Kdjm4pfI_qUV3jdHqyRninesHCuWRrnGyjYauV258eBSiiFePcfII0JE9ObJkZUMmYFqVv2QOftkK2dT-OX01cP7xrL7AShQPdaAURVlNoOsXSuU0oLcbpwsygBpn6kjPUad8D0vODh8ss_IbgaCl6r1wFL0T3Ntyi2Hm5qA
ca.crt: 1099 bytes
五、绑定全局命名空间查看权限
[root@k8s-master01 study]# vim namespace-readonly-sa.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: namespace-readonly-sa
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: namespace-readonly
subjects:
- apiGroup: rbac.authorization.k8s.io
kind: Group
name: system:serviceaccounts:kube-users
[root@k8s-master01 study]# kubectl create -f namespace-readonly-sa.yaml
六、在Master01节点上查看端口号,观察到端口号为30757
[root@k8s-master01 study]# kubectl get svc kubernetes-dashboard -n kubernetes-dashboard
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
kubernetes-dashboard NodePort 10.0.90.127 <none> 443:30757/TCP 9d
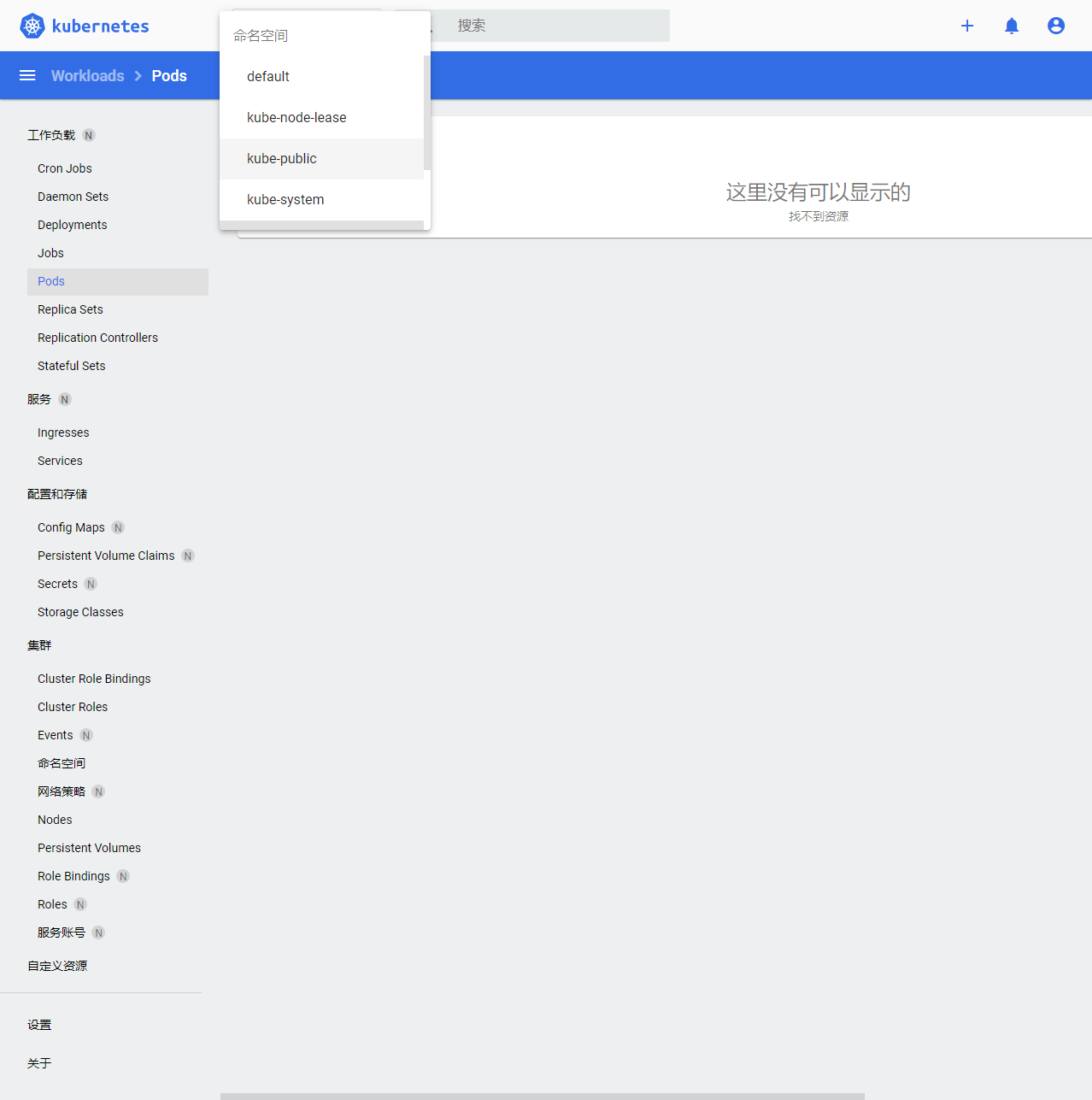
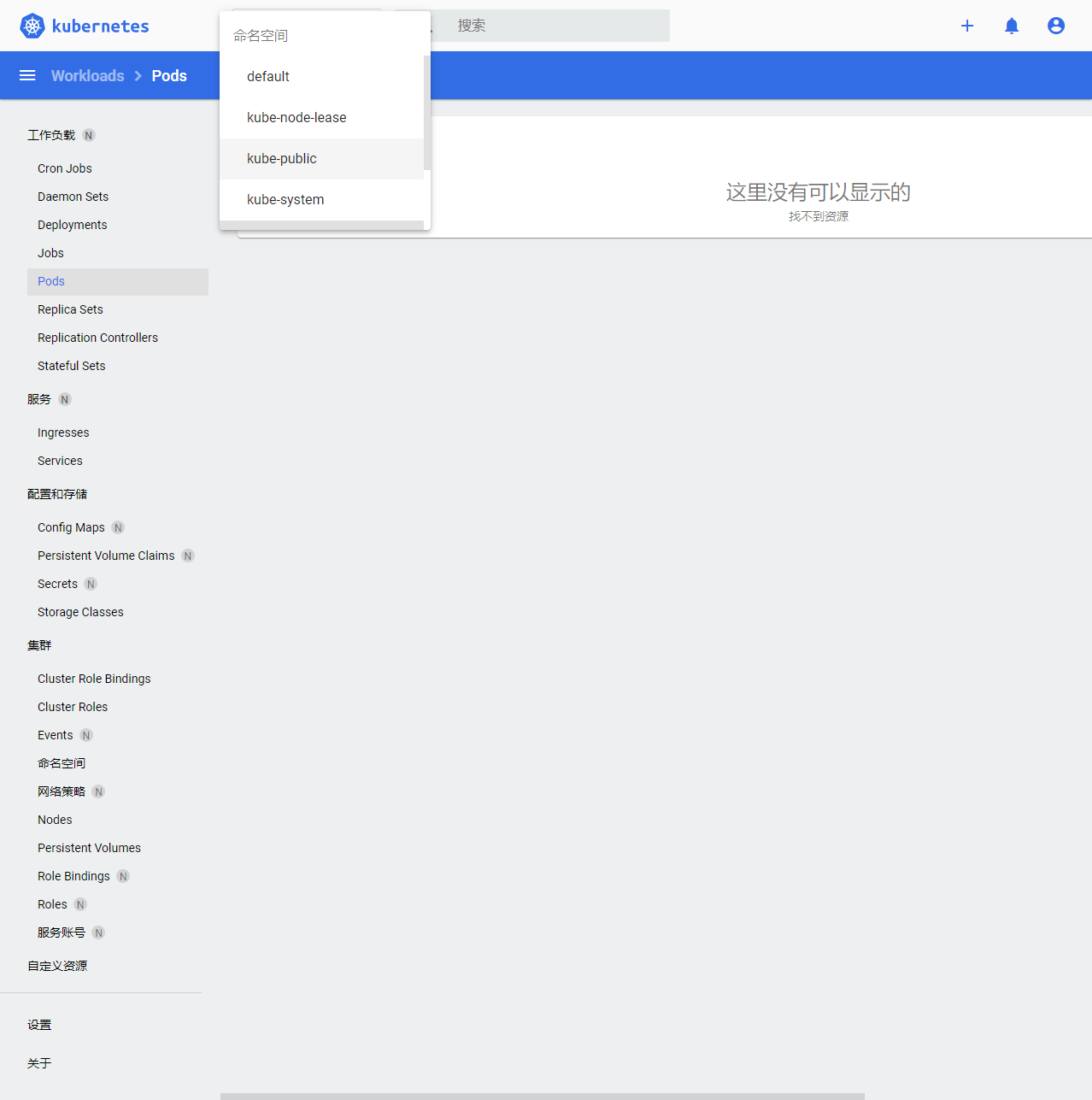
七、使用IE浏览器输入https://192.168.100.31:30757/登录dashboard,token如上。观察到已经可以切换命名空间,其他没权限
八、赋予用户user1可以查看default、kube-system下Pod的日志权限
[root@k8s-master01 study]# kubectl create rolebinding user1-pod-log --clusterrole=pod-log --serviceaccount=kube-users:user1 --namespace=kube-system
[root@k8s-master01 study]# kubectl create rolebinding user1-pod-log --clusterrole=pod-log --serviceaccount=kube-users:user1 --namespace=default
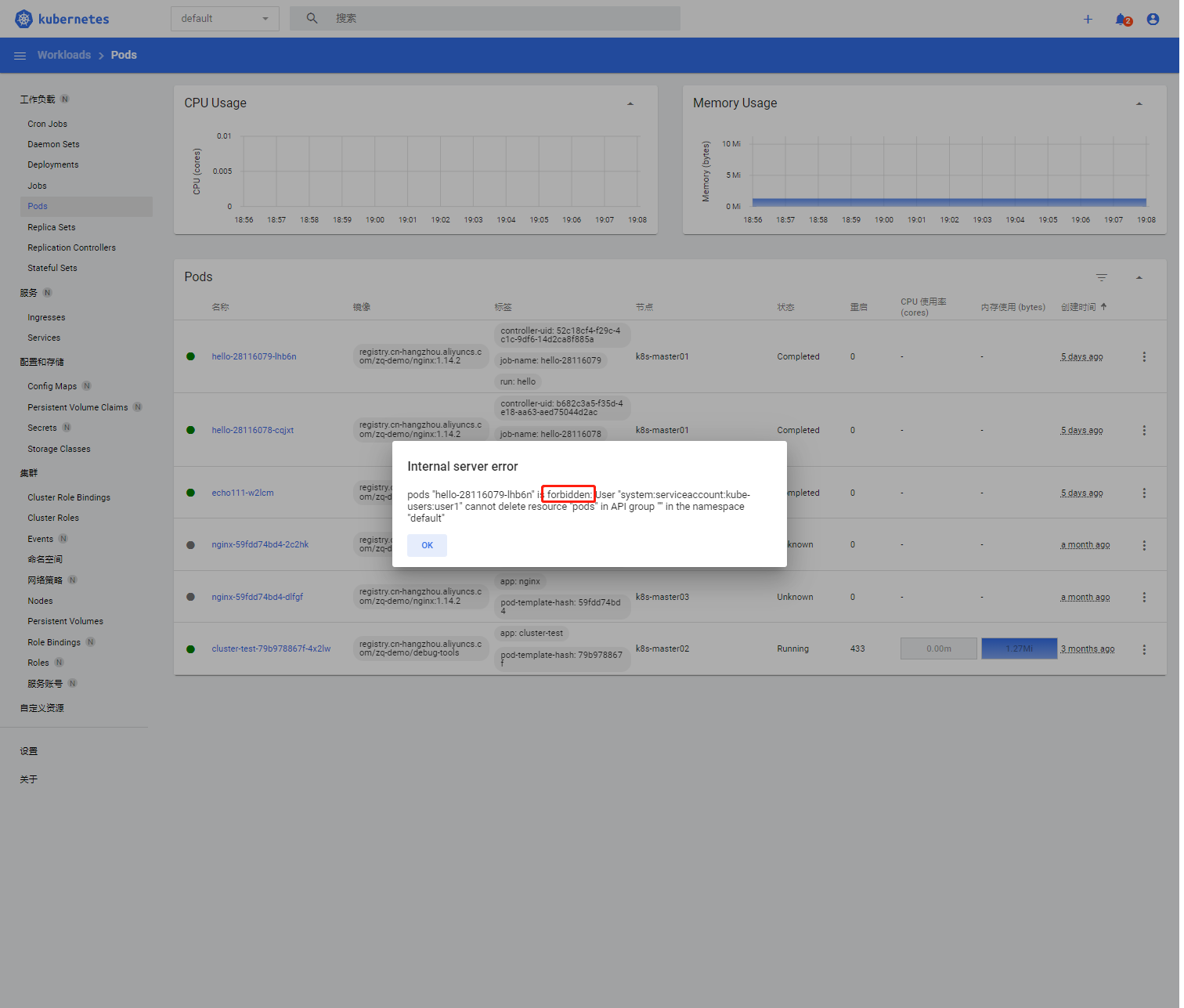
九、使用IE浏览器输入https://192.168.100.31:30757/登录dashboard,输入用户user1的token。操作后观察到用户user1只可以查看default、kube-system下Pod的日志,其他做不了
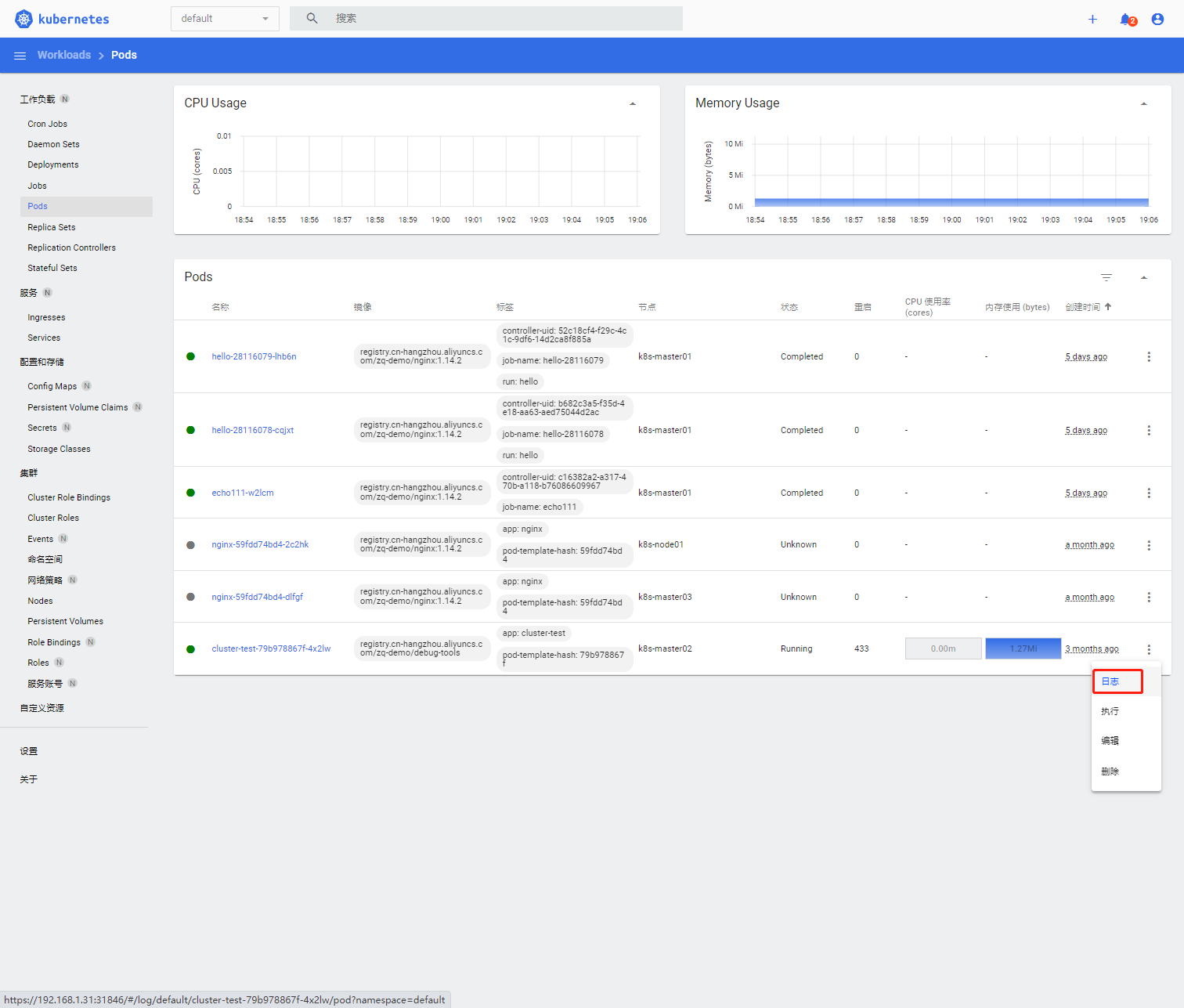
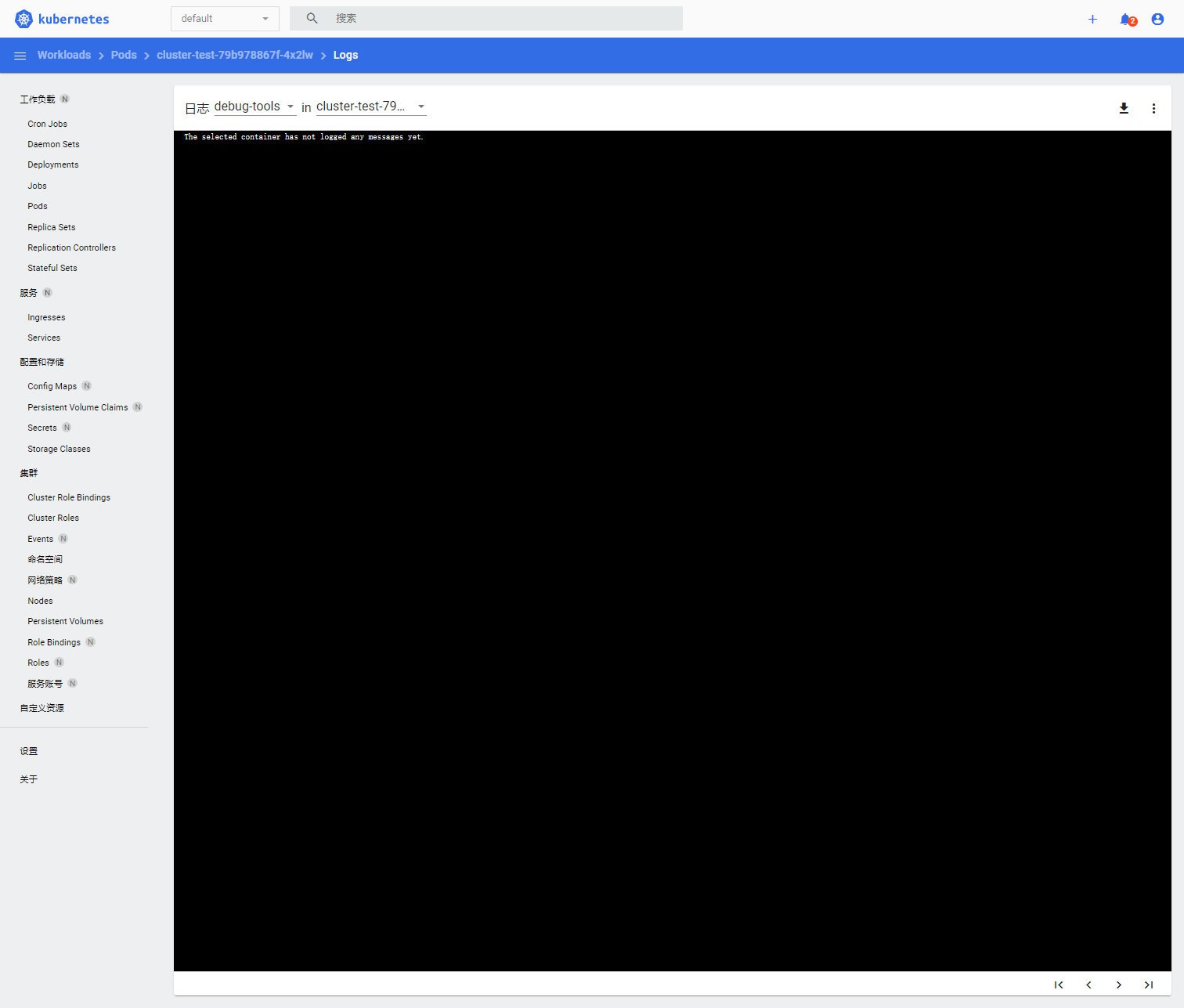
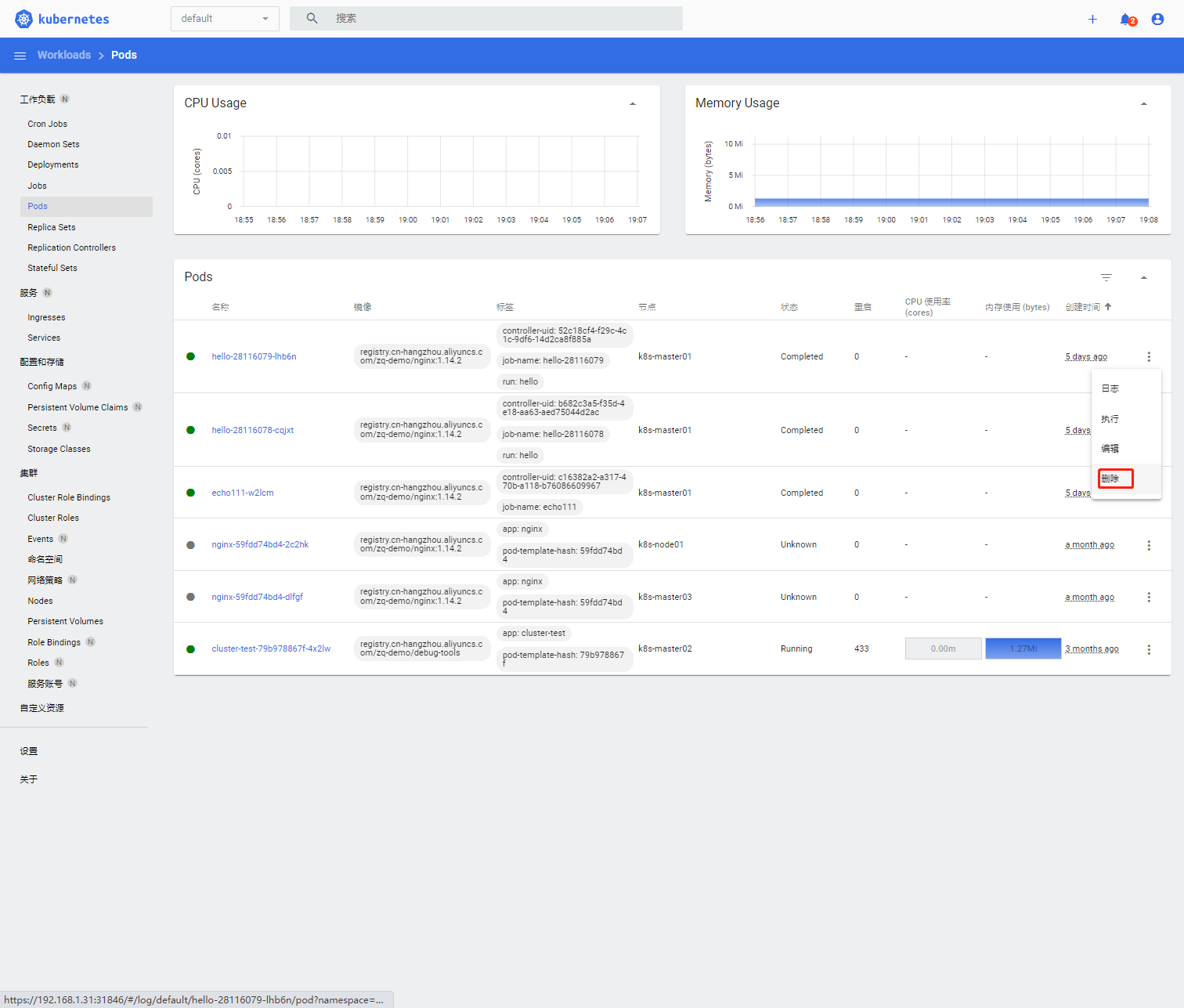
接下来做个测试:尝试删除default命名空间下的pod,结果显示无权限删除
十、赋予用户user2可以在default下的Pod中执行命令,并且可以删除Pod权限
[root@k8s-master01 study]# kubectl create rolebinding user2-pod-exec --clusterrole=pod-exec --serviceaccount=kube-users:user2 --namespace=default
[root@k8s-master01 study]# kubectl create rolebinding user2-pod-delete --clusterrole=pod-delete --serviceaccount=kube-users:user2 --namespace=default
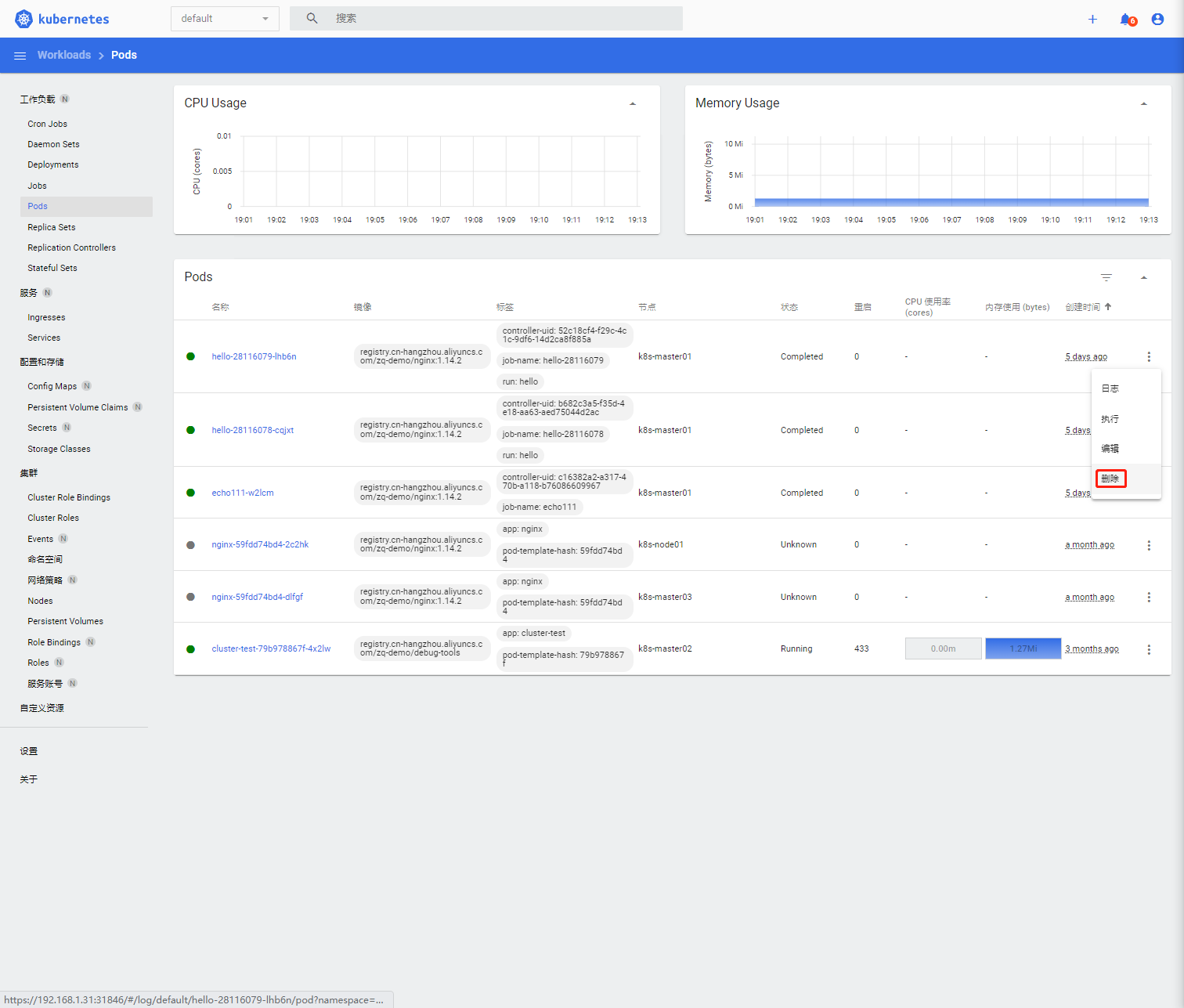
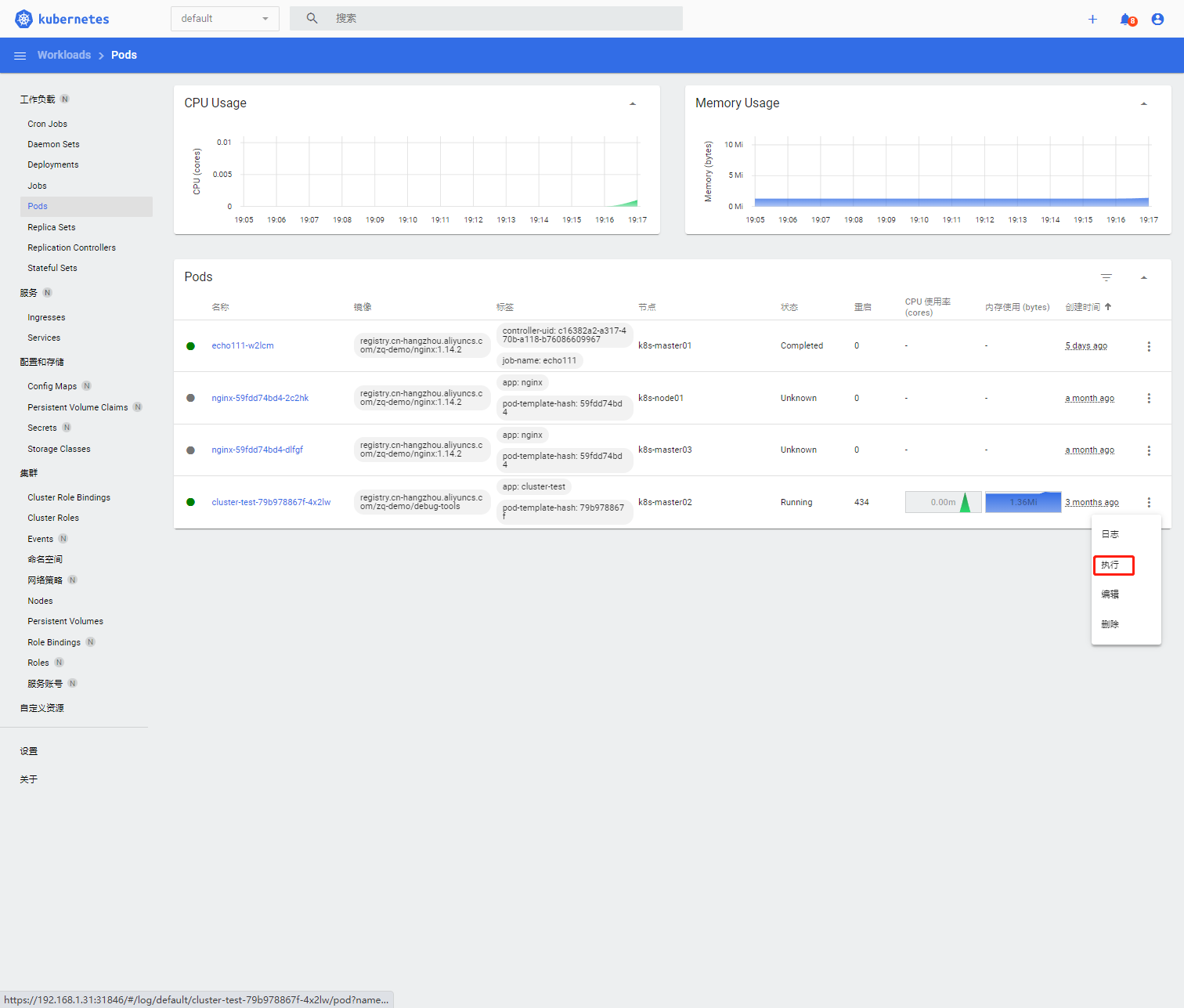
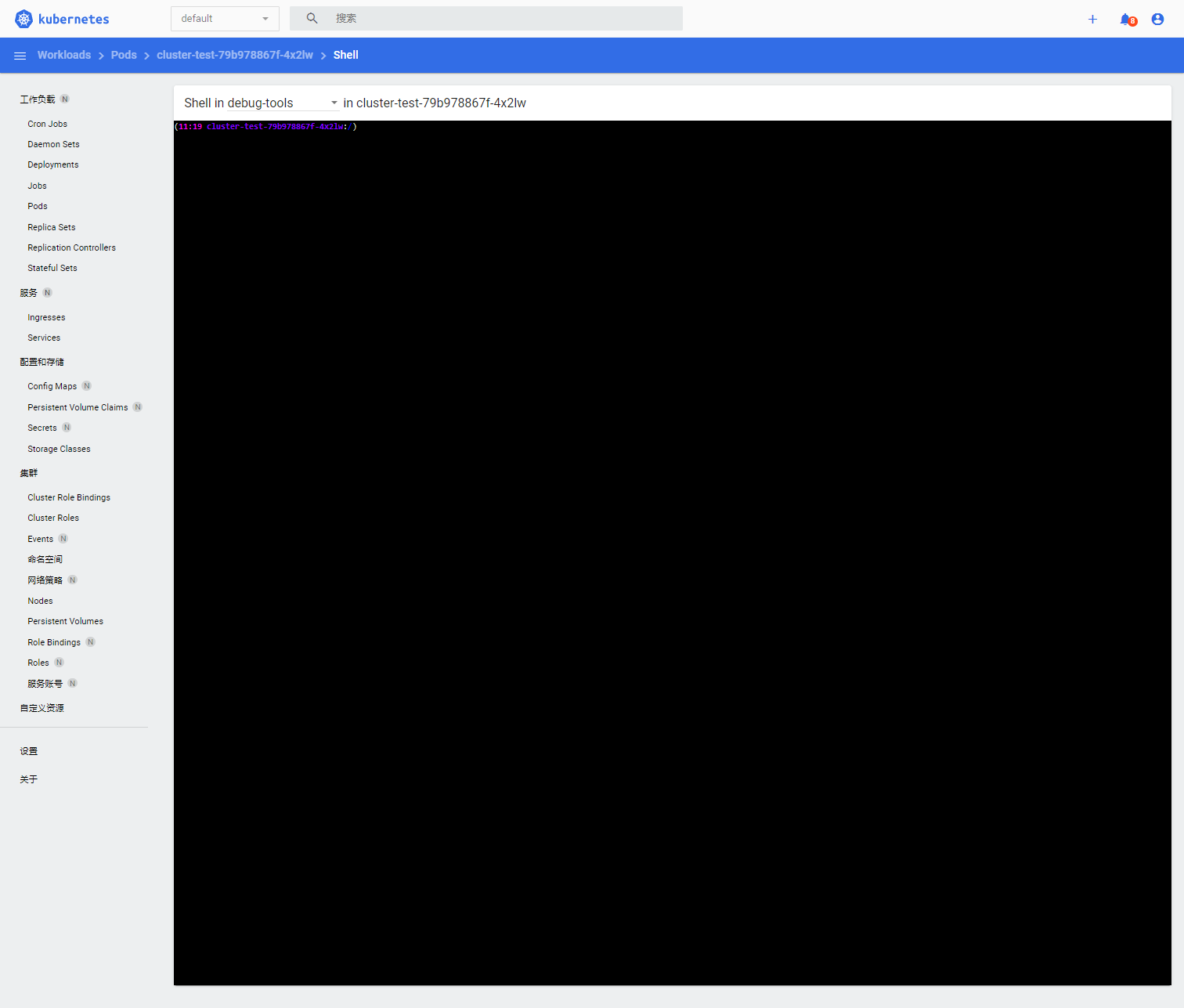
十一、使用IE浏览器输入https://192.168.100.31:30757/登录dashboard,输入用户user2的token。操作后观察到用户user2在default下的Pod中执行命令,并且可以删除Pod权限
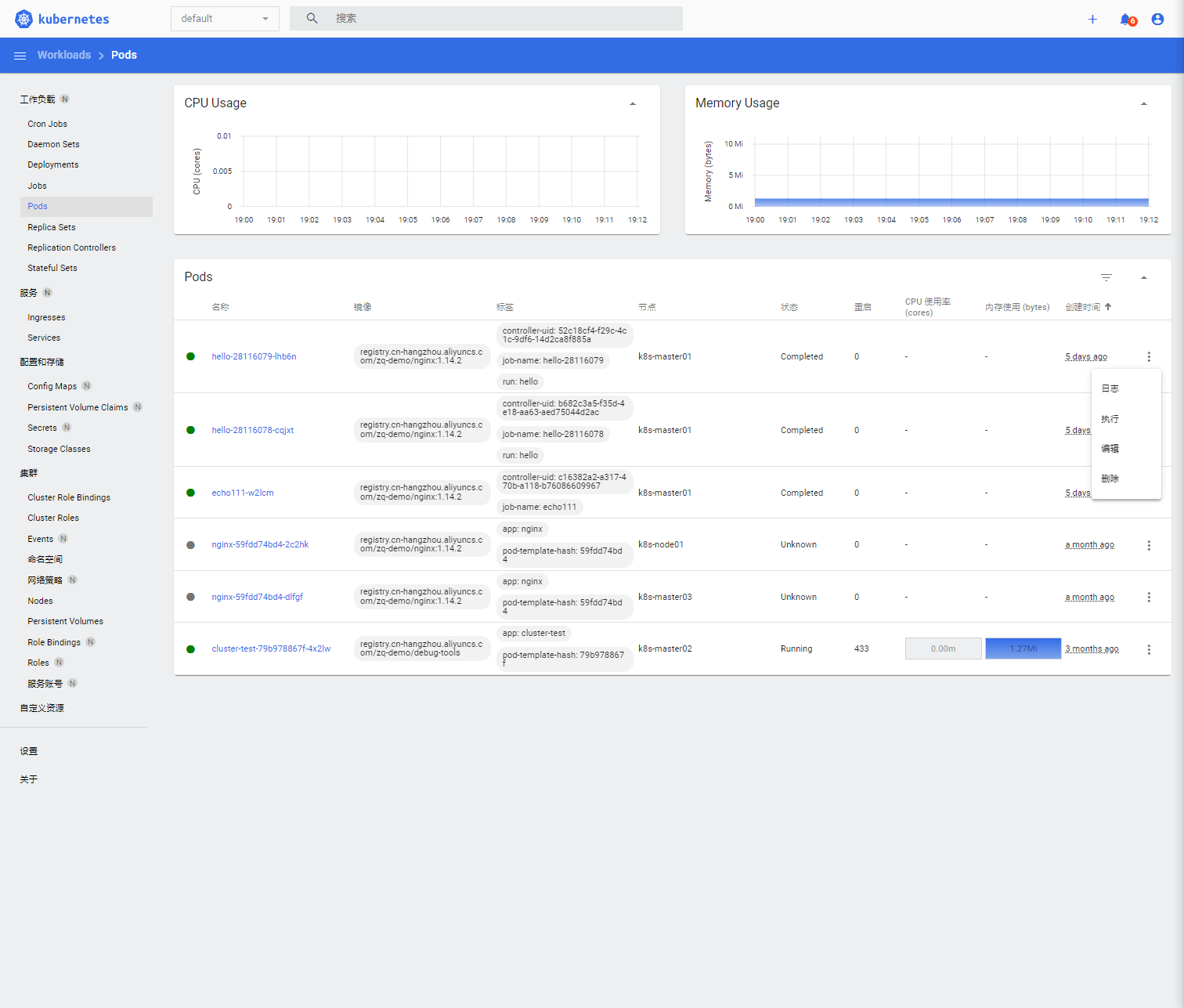
在default下测试pod是否能删除,观察到Pod可以被成功删除
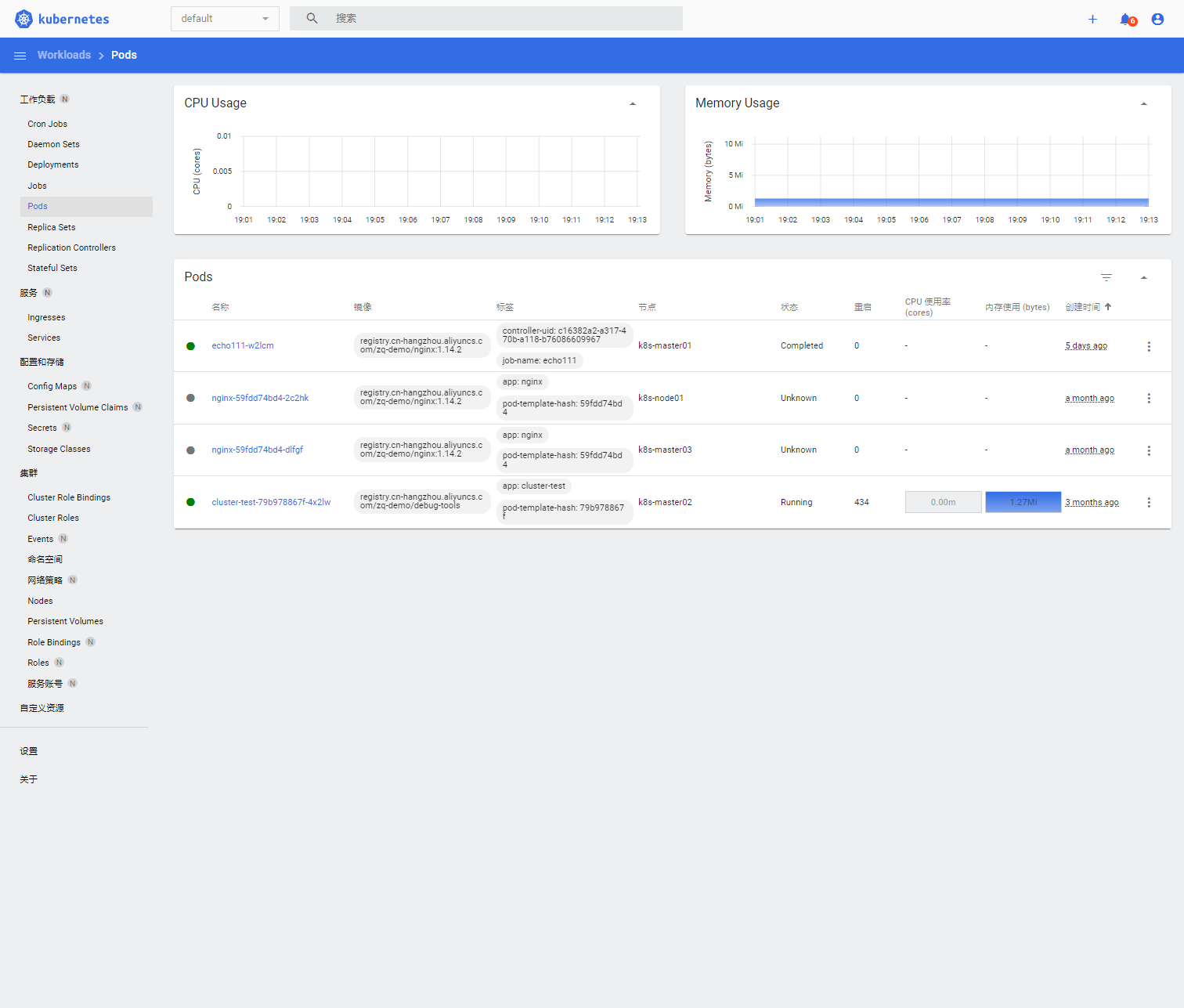
在default下测试pod是否可以执行,观察到Pod可以被成功执行
© 版权声明
文章版权归作者所有,未经允许请勿转载。
THE END







暂无评论内容